IAM, Roles, and Least Privilege
Summary
This note explains the role of identity and access management in cloud environments. The goal is to understand why permissions, roles, and scope are some of the most important parts of safe cloud work.
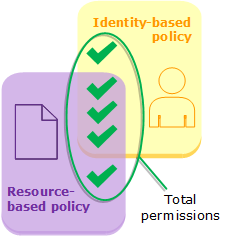
Official AWS diagram showing how different policy layers combine into the effective permissions a cloud identity ends up with.
Why this matters
- many cloud issues are access and permission issues in disguise
- weak IAM design creates both security risk and operational confusion
- cloud roles, service identities, and permission boundaries appear in AWS, Azure, and other platforms
Environment / Scope
| Item | Value |
|---|---|
| Topic | cloud access control basics |
| Best use for this note | understanding cloud permission design |
| Main focus | IAM, roles, scope, least privilege |
| Safe to practise? | yes |
Key concepts
- IAM - identity and access management
- Role - a defined set of permissions used by a user, service, or workload
- Least privilege - giving only the access that is actually needed
- Scope - where and how broadly a permission applies
Mental model
Think about cloud IAM like this:
identity -> role or permission assignment -> allowed actions on resourcesThe main question is not only “does it work?” but also “does it have more access than it needs?”
Everyday examples
| Situation | IAM question |
|---|---|
| app needs to write logs | what is the smallest permission set needed? |
| pipeline deploys infrastructure | what should the deployment identity be allowed to change? |
| user can access too many resources | is scope too broad? |
| function or app fails to reach a service | does its role actually allow that action? |
Common misunderstandings
| Misunderstanding | Better explanation |
|---|---|
| ”If permission works, the IAM design is fine” | overbroad access can still be a serious issue |
| ”Least privilege means painful administration” | it usually means more deliberate permission design |
| ”Roles only matter for users” | workloads and services often rely on roles too |
| ”Permission denied always means cloud is broken” | it often means the role design is incomplete or wrong |
Verification
| Check | Expected result |
|---|---|
| Access path is clear | you know which identity is acting |
| Scope is sensible | permissions are not broader than needed |
| Workload can do required task | role is sufficient for intended actions |
| Denials are explainable | failures make sense in the IAM model |
Pitfalls / Troubleshooting
| Problem | Likely cause | What to check |
|---|---|---|
| Access denied | missing or wrong role | effective permissions |
| Everything works but risk feels high | overbroad role | scope and least privilege |
| Deployment pipeline is too powerful | convenience-based permission design | role boundaries |
| Troubleshooting feels confusing | identity acting path is unclear | user vs service identity |
Key takeaways
- IAM is both a security topic and an operational topic
- least privilege improves both safety and explainability
- many cloud failures make more sense once you trace the identity and role path first